Trezor Login: Your Secure Gateway to Crypto Safety
Everything you need to know about accessing, managing, and protecting your crypto through Trezor Login.
🔑 What is Trezor Login?
Trezor Login is the official access process that connects your Trezor hardware wallet to trusted interfaces such as Trezor Suite. It ensures your private keys never leave your device, maintaining top-tier protection against online attacks or phishing attempts. When you use Trezor Login, your crypto stays safe, offline, and fully under your control.
🪜 Step-by-Step Trezor Login Setup
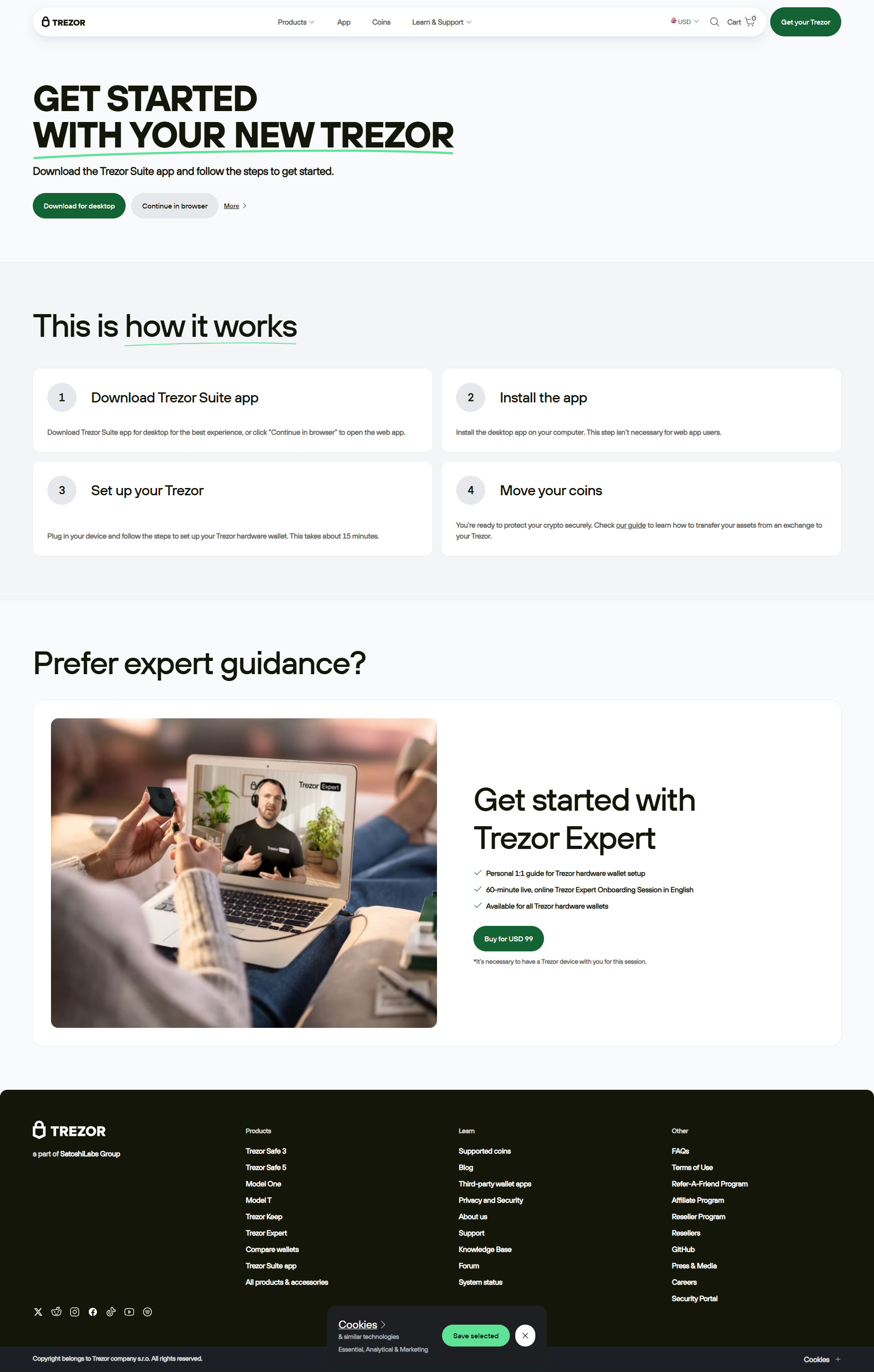
Step 1: Visit Trezor.io/Start
Always start your journey by visiting the official Trezor setup page. This ensures your firmware, apps, and software are genuine and secure.
Step 2: Connect Your Device
Plug in your Trezor Model T or Trezor One using the provided USB cable. Your computer should automatically detect it through Trezor Suite.
Step 3: Install Trezor Suite
Download and install Trezor Suite, the official desktop and browser-based platform for managing your crypto portfolio.
Step 4: Authenticate and Access
Once connected, click “Login with Trezor.” You’ll confirm the login on your device screen — a vital step ensuring your session is verified.
💡 Why Trezor Login is the Safest Way to Access Crypto
Unlike software-based wallets that rely on passwords or cloud data, Trezor Login uses secure hardware encryption. This means your login credentials never touch the internet, making it virtually impossible for hackers to gain access to your funds.
🛡️ Hardware Security
Trezor’s cryptographic chip ensures private keys are stored offline, out of reach from malware and keyloggers.
🌐 Trusted Connection
Only verified websites and apps can interact with Trezor through end-to-end encrypted communication channels.
🔍 Transparency
Trezor’s open-source architecture means every part of the software can be audited for security and privacy.
📱 Trezor Login via Trezor Suite
The Trezor Suite is your command center for all things crypto. It offers a unified interface for portfolio tracking, transaction signing, and firmware updates — all managed through the secure Trezor Login process.
- Access your entire crypto portfolio in real time.
- Send and receive coins securely using your device for confirmation.
- Update firmware and coin support seamlessly.
- Integrate Trezor with wallets like MetaMask and Electrum safely.
⚖️ Trezor Login vs Software Wallet Login
| Feature | Trezor Login | Software Login |
|---|---|---|
| Private Key Storage | Offline (inside Trezor chip) | Online or in local files |
| Security Risk | Extremely low | High (vulnerable to malware) |
| Authentication | Device-confirmed login | Password only |
| Transparency | Open-source firmware | Closed-source software |
🧠 Troubleshooting Common Login Issues
Issue 1: Device not recognized by computer.
Fix: Use the original USB cable, update Trezor Bridge, and restart Trezor Suite.
Issue 2: Login button not responding.
Fix: Refresh Trezor Suite or clear browser cache if using web version.
Issue 3: Forgot PIN or passphrase.
Fix: Reset the device and restore from your recovery seed phrase.
❓ Frequently Asked Questions (FAQ)
Q1: Is Trezor Login safe for beginners?
A: Yes, it’s designed for simplicity while maintaining enterprise-level security.
Q2: Can I log in from any computer?
A: Yes, as long as you have your Trezor device and Trezor Suite installed, your keys stay protected.
Q3: What happens if I lose my Trezor device?
A: You can restore all your assets using your 12–24 word recovery phrase on a new device.
Conclusion: Trezor Login – The Future of Safe Crypto Access
Trezor Login isn’t just a way to access your crypto — it’s a security revolution. With hardware-level encryption and intuitive control via Trezor Suite, users can manage digital assets confidently, knowing their keys never leave their hands.